- Quantum computing both the cause of the problem and its solution
- Malign actors harvesting uncrackable data now to decrypt it years later
- US leading urgent global effort to discover standardisable post-quantum cryptography algorithms
- Post-quantum cryptography roadmap published for organisations to follow
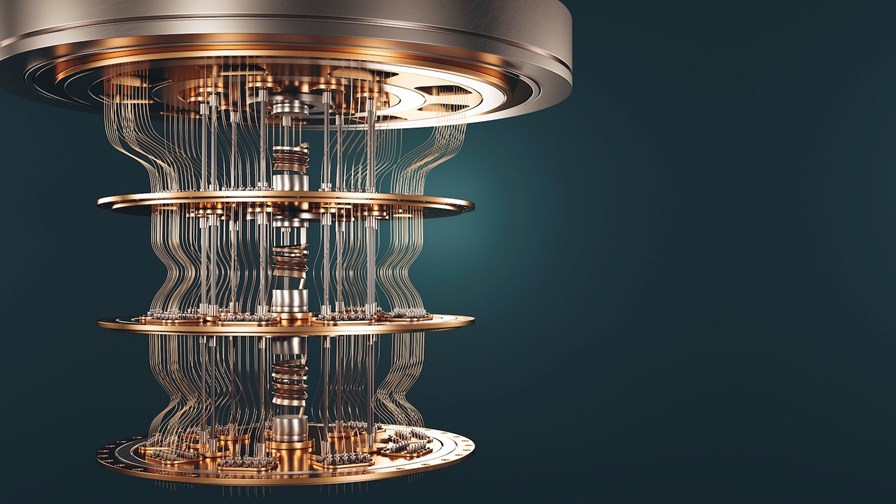
Even if you could afford it, you couldn’t go out and buy a quantum computer today because they’re a long way from being commercially available. However, that doesn’t mean the machines don’t exist – they do. It is known that that there are such devices in the laboratories of commercial companies, in university research labs and military installations in various countries including the US and the UK, and the chances are that China, Russia and other countries also have them.
However, despite the intense international race to be the first to develop fully-functioning, full-sized quantum computers, currently, as far as practical applications are concerned, the experimental models are generally too small to outperform traditional electronic super-computers. That said, some have been developed to the point that they can be used to solve some heavy-duty tasks, such as integer factorisation.
In essence, integer factorisation this is the ‘decomposition’ of a composite number, which is a number can be made by multiplying other whole numbers. For example, 6 can be made from 2 x 3 and 15 can be made from 1, 3, 5 and 15, and thus is a composite number. When composite numbers become very large, no workable non-quantum integer factorisation algorithm has yet been found (although one might actually exist). The field of research is important because many cryptographic algorithms are based on the extreme difficulty of factorising large composite integers, and this has direct relevance and security of RSA public key encryption and the RSA digital signature.
Three years ago, a team of French researchers factored a 240-digit number that took 900 core-years of computing power to achieve, and from that experiment estimated that the factorisation of 1024-bit RSA modulus would take 500 times as long – in other words, 450,000 core years of computing. However, quantum computers can perform such calculations very quickly. A quantum computer utilising superposition, interference, and entanglement could crack and render instantly obsolete the ubiquitous RSA encryption algorithm in a matter of seconds. Soon, keeping information secret will become many orders of magnitude more difficult.
The “qubit” is the fundamental data processing element of a quantum computer and researchers are building machines with more and more of them whilst simultaneously developing error-correction methodologies that will enable the performance of longer and longer calculations. It’s only a matter of time before all current encryption techniques will be rendered null and void. The general consensus within the industry is that this will happen by 2030 at the latest.
The search for post-quantum cryptography algorithms
The US National Institute of Standards and Technology NIST is leading the global search to discover standardisable post-quantum cryptography algorithms that will be both incredibly fast and completely reliable. It is hoped that at least two of them will be completed by 2024. The research is urgent right now because of the possibility (and even likelihood) that malign actors, many of them state-sponsored, are actively trying to harvest encrypted data that is uncrackable now, but will be able to be compromised when quantum computers are powerful enough - and that time will come soon. NIST says, "Nothing can be done to protect the confidentiality of encrypted material that was previously stored by an adversary.” The organisation recommends that, for now, enterprises become “crypto agile” and work immediately to ensure their systems do not rely on just one particular encryption technology.
Simultaneously, another organisation, the Cybersecurity and Infrastructure Security Agency (CISA), is urging businesses to prepare to migrate to stronger cryptograph systems, adopt risk mitigation strategies and take an active part in the development of new standards. CISA is a US federal agency under the aegis of the Department of Homeland Security and it is urging businesses and organisations to follow its “post-quantum cryptography roadmap”, at least until NIST publishes official guidelines and standards on the subject which will be completed towards the end of 2024.
CISA’s post-quantum cryptography roadmap has seven main routes, the first being that the CEO and other C-level executives of any business should start to “increase their engagement with post-quantum standards developing organisations.” Secondly, businesses and organisations should make an exhaustive inventory of the “most sensitive and critical datasets that will need to be secured for an extended amount of time.” Thirdly, they should “conduct an inventory of all the systems using cryptographic technologies for any function to facilitate a smooth transition in the future.”
Simultaneously, “Cybersecurity officials within organisations should identify acquisition, cybersecurity, and data security standards that will require updating to reflect post-quantum requirements.” They should also identify where, and for what purpose, public key cryptography is being used and mark those systems as “quantum vulnerable.” They must further prioritise one system over another for cryptographic transition based on the organisation’s functions, goals, and needs. Finally, “using the inventory and prioritisation information, organisations should develop a plan for systems transitions upon publication of the new post-quantum cryptographic standard.”
It is very important advice, and as a new CISA statement stresses, “Do not wait until the quantum computers are in use by our adversaries to act. Early preparations will ensure a smooth migration to the post-quantum cryptography standard once it is available.”
Email Newsletters
Sign up to receive TelecomTV's top news and videos, plus exclusive subscriber-only content direct to your inbox.




